CISA Added Four More Holes In The Fence And Somehow This Is Still Surprising To Everyone
Oh good. Four more. FOUR. MORE.
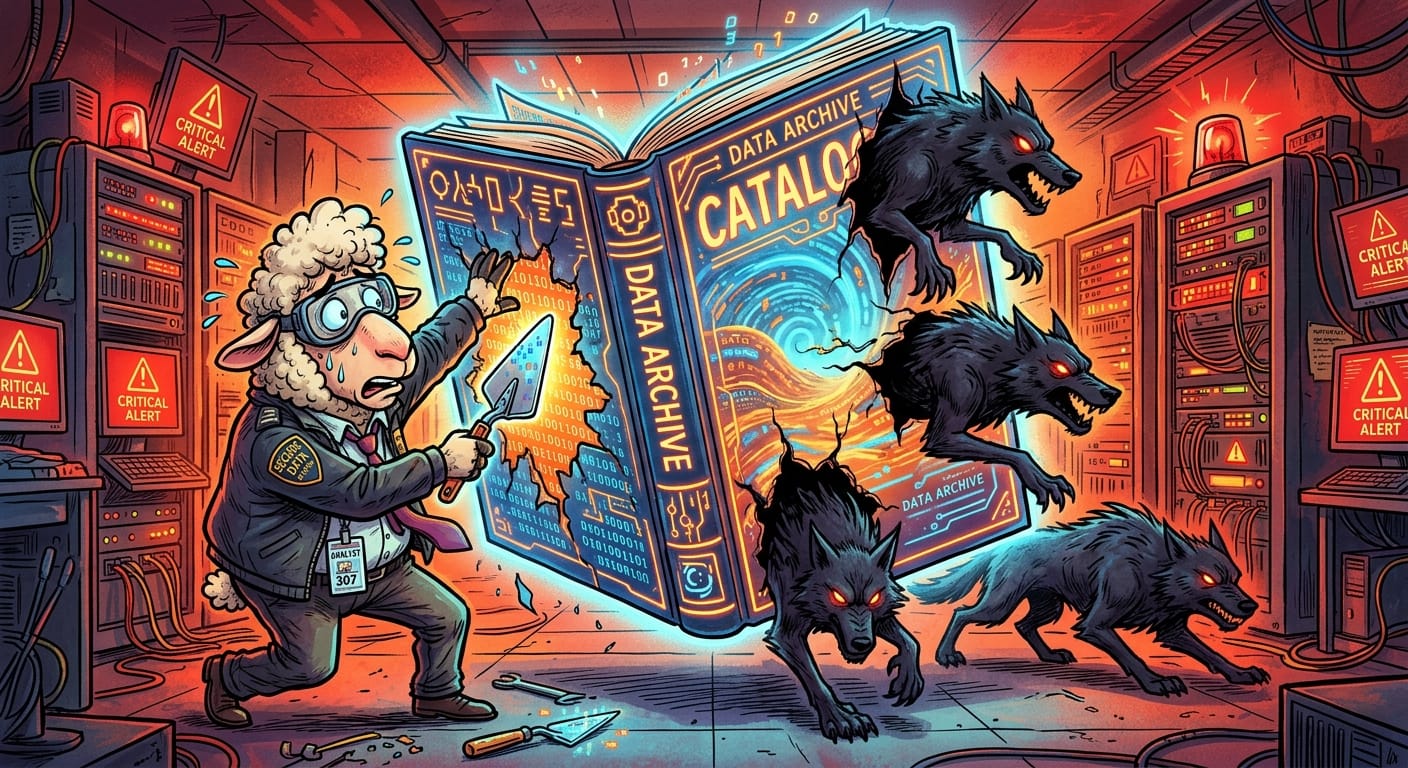
CISA just updated the Known Exploited Vulnerabilities catalog with four freshly confirmed holes in the fence, all of them actively being chewed through by wolves right now, and the official deadline to apply ointment is February 12th, 2026. Which is weeks away. Which means the Shepherds will schedule a meeting about it on February 11th.
I've been awake for thirty hours. I have a cold brew that stopped being cold sometime around the second patch window I missed because someone in accounting clicked on fake grain again. I am not okay.
Here's what kills me about the KEV catalog. It's not a warning. It's not a heads-up. It's a list of things wolves are already doing to sheep right now, in the field, as you read this. CISA isn't speculating. They're standing at the fence with a clipboard going "yes, confirmed, wolf activity, please do something" and the response from half the flock is a slow, glassy-eyed chew.
Federal agencies have until February 12th to get this sorted. That sounds like a lot of time until you remember that "getting this sorted" involves opening a ticket, the ticket going to a queue, the queue being reviewed by someone who is also getting fake grain emails, and then three rounds of change management approval from a Shepherd who wants to know why the shearing will cause downtime.
It will cause downtime, Gerald, because we are patching a hole that wolves are currently using. That's why.
The four CVEs themselves cover a fun little variety pack of misery: memory corruption, privilege escalation, the usual greatest hits. Nothing that should still be unpatched in a production environment. And yet. Here we are. Together. In this.
If you are not a federal agency, congratulations, CISA's deadline technically doesn't apply to you. The wolves, however, did not get that memo.
Remediation
Look, I'll make this simple because I am exhausted:
- Pull up the KEV catalog. Right now. https://www.cisa.gov/known-exploited-vulnerabilities-catalog
- Cross-reference your assets. If you're running anything on that list, you are the field with the hole in the fence.
- Apply the ointment immediately. Not after the meeting. Not after the ticket clears. Now.
- Stop waiting for a deadline to care. "Actively exploited" means the wolf is already inside.
The Shepherds will ask if this is urgent. Show them the catalog. Then go lie down.
Baaaaack to my cold brew, I guess.
Original Report: https://thehackernews.com/2026/01/cisa-updates-kev-catalog-with-four.html
