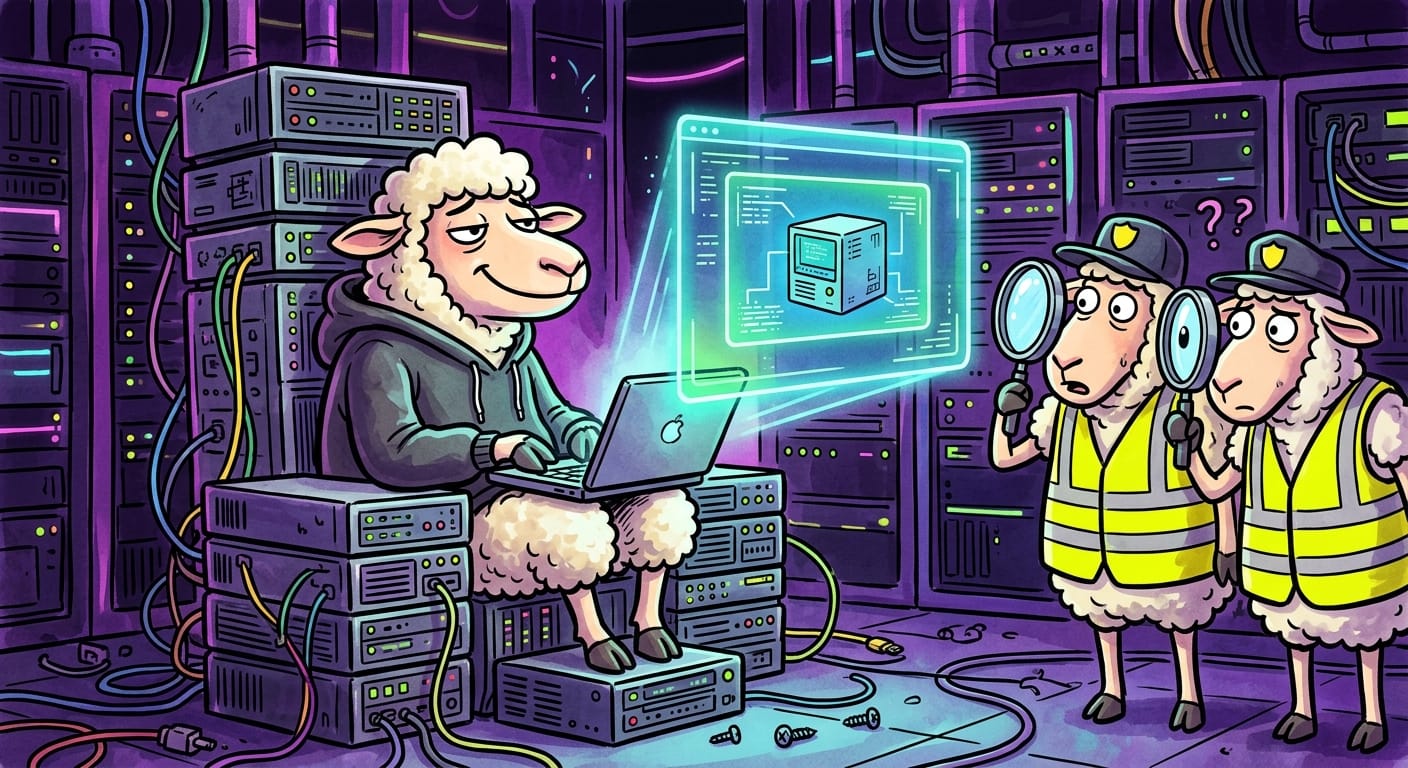
The Wolves Brought Their Own Barn. Inside Your Barn.
I need you to really sit with this one for a second.
The Payouts King crew, which is already a name that makes me want to retire and become an actual shepherd, has figured out that your electric fence only watches what's on your field. So they just... built a second, invisible field inside your field. Using QEMU to spin up hidden virtual machines on compromised systems, then running a reverse SSH backdoor through the whole thing.
Your endpoint detection is sitting there, tail wagging, reporting "all clear," while a fully operational wolf den is humming away in the basement.
I'm so tired.
The genius, and I say that through gritted teeth, is that QEMU is legitimate software. It's a real tool that real sysadmins use. So when the electric fence sees it, the fence goes "oh that's fine, that's a known grazing application," and waves it through. The parasites then run their entire operation inside the VM, completely shielded from your security tooling.
The reverse SSH piece is what really made my coffee taste like ash this morning. The connection goes outbound from the compromised host, so there's no suspicious inbound traffic to flag. The wolf isn't knocking on the door. The wolf is calling from inside the house. Using your phone. On your plan.
Now, did the flock help with initial access? Almost certainly yes. Fake grain, a suspicious attachment, a link that definitely said "click here for free hay." The lambs never disappoint.
The shepherds, naturally, have already asked me if this is covered by our current vendor contract.
Remediation
Look. I know you're tired too. Here's what actually matters:
Block QEMU where it doesn't belong. Application whitelisting. If your accounting department doesn't need a hypervisor, they don't get one. This is not a negotiation.
Monitor for unexpected outbound SSH. Reverse tunnels are sneaky but they still make noise if you're actually watching. Set up egress filtering and alert on SSH traffic from hosts that have no business making it.
Shear your systems regularly. Unpatched endpoints are how the wolves get in to set up their little virtual real estate in the first place. Patch. Actually patch. Not "we'll get to it in Q3."
Hunt for QEMU processes in weird places. Run a sweep now. Not after the incident report.
Segment the pasture. If one lamb is compromised, the rest of the flock shouldn't be reachable from inside a secret VM running on that lamb's laptop.
None of this is fun. None of it will get you a thank-you card.
Go drink some water, I guess, we're all going to be here a while.
Original Report: https://www.bleepingcomputer.com/news/security/payouts-king-ransomware-uses-qemu-vms-to-bypass-endpoint-security/
