The Wolves Poisoned the Watering Hole and Honestly??? The Audacity 😤🐑
Okay so I am FERAL right now. Like, I woke up, checked my feeds, and nearly choked on my matcha because the CPUID situation is genuinely sending me to another dimension. No cap.
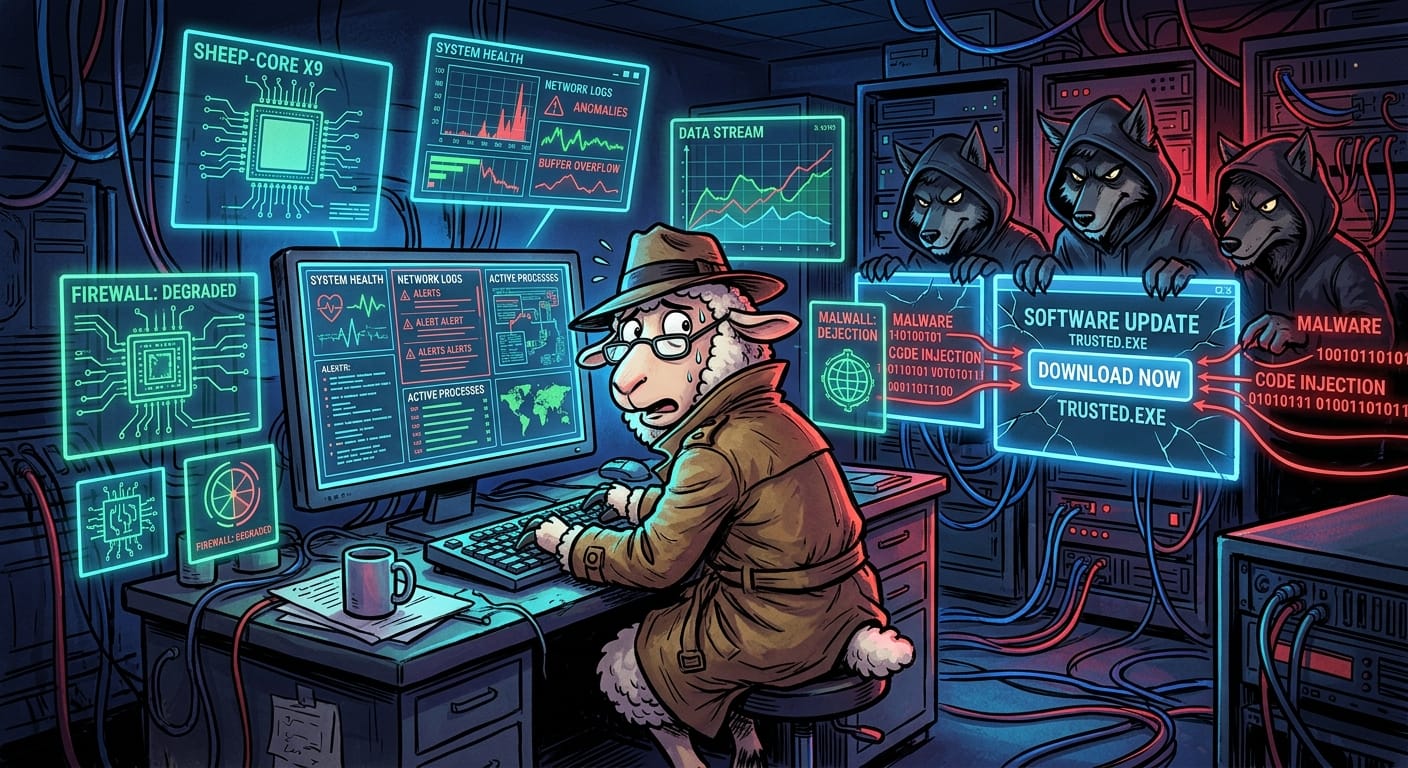
So here's the tea: some absolute coyote energy individual slithered into CPUID's API, changed the download links on the official website, and suddenly CPU-Z and HWMonitor are handing out fleas and ticks like party favors. The flock just walked right up to the watering hole, took a big sip, and boom. Infested. 😵💫
The cringe factor here is astronomical, bestie. This is a SUPPLY CHAIN attack, which means the wolves didn't even have to do anything dramatic. No elaborate luring, no fake grain campaigns, no sketchy emails. They just... quietly swapped the good grain for poison grain at the source. The lambs trusted the official pasture and got absolutely cooked for it. It's giving "betrayal arc" and I hate it.
What makes this extra unhinged is that your Electric Fence is basically useless here. Your security tools see a download from the legitimate official site and go "slay, looks fine!" because technically? It IS the legitimate site. The wolves wore the shepherd's clothing and nobody clocked it until it was too late. Embarrassing behavior from the threat landscape, honestly. #SupplyChainSzn #NotOkay
The Shepherds in your org are probably still in a meeting debating the Q4 Sky Pasture migration budget right now, completely unbothered. Classic. 🐑💤
This is why I have TRUST ISSUES with software downloads and I will not be taking questions.
💊 Remediation: Okay Bestie Here's What We Do
- Verify your hashes, period. Before any software touches your flock's machines, check the cryptographic hash against a KNOWN GOOD source. Not the same compromised website. A different source. Use your brain cells. 🧠
- Application allowlisting is the move. If it's not on the approved list, it doesn't graze in this pasture. End of discussion.
- Monitor for weird parasite behavior. Endpoint detection tools should be screaming if freshly downloaded software starts doing suspicious things post-install. If they're not, your Electric Fence needs serious shearing.
- Audit your third-party dependencies. Every external tool is a potential hole in the fence. Treat them accordingly. Zero trust, no cap.
- Tell the Shepherds. Yes even though they won't understand it. Especially because they won't understand it.
Stay paranoid, stay hydrated, and maybe just... build everything from source at this point idk 🐑✨ #EwePhoria #StayVigilantSlay
Original Report: https://www.bleepingcomputer.com/news/security/supply-chain-attack-at-cpuid-pushes-malware-with-cpu-z-hwmonitor/
