ZionSiphon: When The Wolves Come For The Watering Hole
I have been warning about this for fifteen years. Fifteen years of memos, of conference presentations, of strongly-worded emails to Shepherds who were too busy approving cloud migration budgets to read them. And here we are.
ZionSiphon. A set of parasites engineered specifically to infiltrate operational technology systems inside water treatment and desalination facilities. Not your garden-variety fleas looking for a quick payday. This is purpose-built sabotage code. Targeted. Patient. Architectural in its malice.
I respect the craftsmanship, professionally speaking. I despise everything else about it.
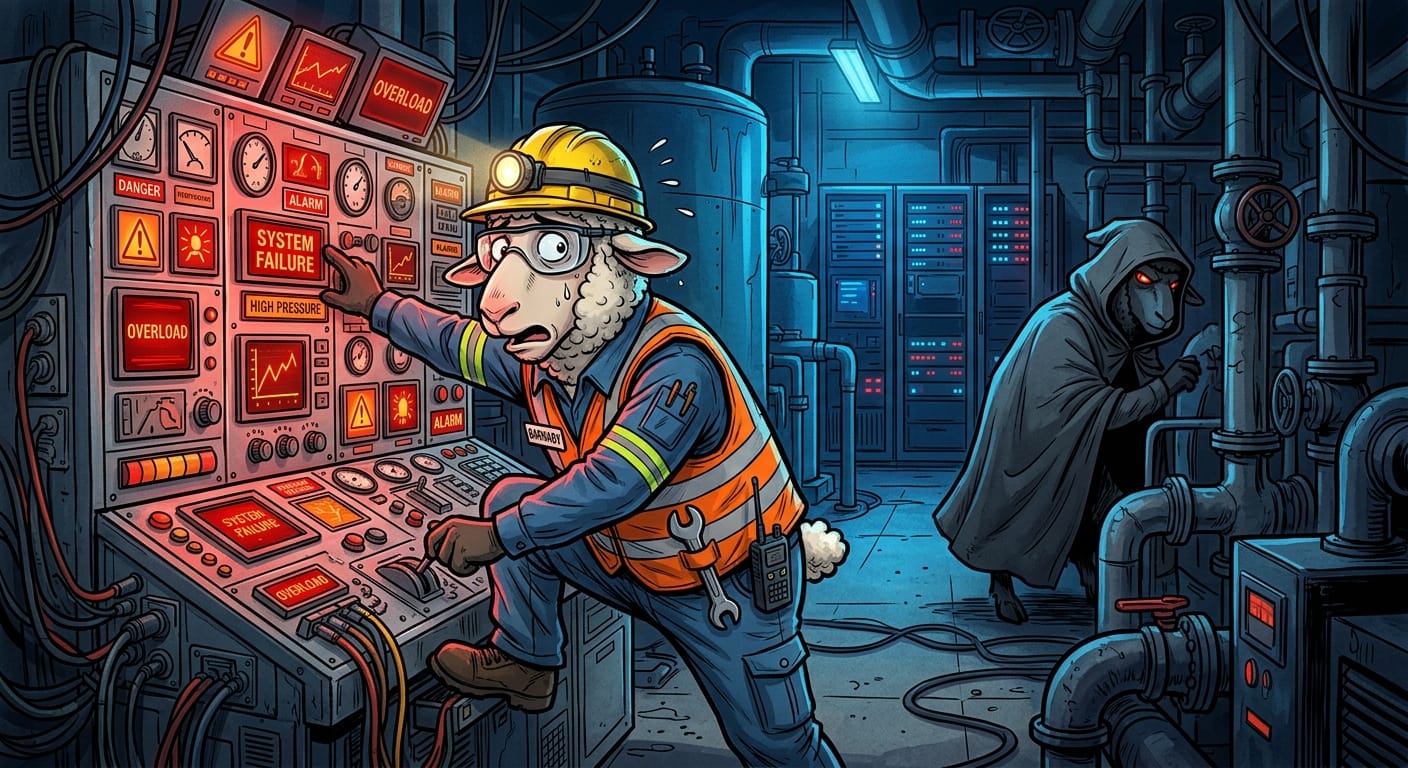
The wolves have stopped chasing individual lambs. They are now poisoning the trough. Do you understand the difference? Because I am not sure the Shepherds do.
Water treatment infrastructure runs on legacy SCADA and industrial control systems. Systems that, frankly, were never designed to be connected to anything resembling the modern internet. In the old days, you wanted to tamper with a water facility, you had to physically be there. Air gaps were not a philosophy, they were a physical reality enforced by geography and magnetic tape. Nobody was tunneling into a pumping station over dial-up because the pumping station was not ON dial-up.
Then someone decided connectivity was progress. Someone always does.
ZionSiphon reportedly targets these OT environments to manipulate or disrupt operational processes. Chemical dosing. Flow rates. The actual physical outputs of critical infrastructure. This is not ransomware asking for cryptocurrency. This is a wolf that does not want your wool. It wants the flock dead.
Modern security tooling, with its cheerful dashboards and its little green checkmarks, is not built for this environment. I have said it before and I will say it until they pry my terminal from my cold, frustrated hands.
Remediation
I will keep this brief because frankly it should be obvious:
Segment your operational technology from your IT network. Completely. No exceptions, no "temporary" bridges for convenience. If your SCADA system can be reached from the same network your Shepherds use to check their email, you have already lost.
Audit every connection into your OT environment. Every Sheep Tunnel, every remote access point, every vendor credential. Assume the hole in the fence is already there. Find it before ZionSiphon does.
Apply your ointment. Industrial control systems are notoriously under-patched because operators fear downtime. The wolves are counting on that fear. Schedule maintenance windows and use them.
Disable what does not need to exist. Unnecessary services, unused ports, default credentials. Remove them. The Electric Fence only works if it covers the whole perimeter.
And for the love of everything, get your Shepherds into a briefing room before someone ends up with a contaminated water supply.
Stay paranoid out there, it is the only rational position.
Original Report: https://www.bleepingcomputer.com/news/security/zionsiphon-malware-designed-to-sabotage-water-treatment-systems/
